In a scenario where owning a smartphone is a must, and having an Internet connection is the norm, we spend a significant part of our lives in the digital world. Biometric solutions play an important role in providing security.
In the online world, we are living a virtual life where we can make friends, engage in conversations with them, make purchases or have fun with different websites or apps. And this is great, but there are some risks involved.
In real life, our security is always among our main concerns. We like to feel safe, and that’s the reason why our doors have keys and our homes have alarms. The same is true in digital environments.
Protecting our information and identity on the Internet has traditionally been performed on a user / password basis. But this mechanism has weaknesses. Using biometrics or tokens as other authentication factors provides an extra security layer, reducing the risk of identity theft.
But which of these two techniques (passwords or biometrics) will mark the future of digital security? Let’s dive into them.
The main issues with passwords
Our computer devices contain a large amount of personal data collected from our digital activity, hence the importance of using security mechanisms to protect it. Passwords were created with the aim of protecting our online information from being accessed by others.
The most effective way to establish secure passwords is by using a combination of alphanumeric digits that are difficult to figure out, and changing them from time to time. This can be a tedious and sometimes impossible task, due to the number of different accounts people have.
But the main problem with passwords is the human factor. Let’s admit it: human beings are imperfect by nature. In the case of passwords, humans are the weakest link in the online security chain. As a consequence, security levels decrease considerably:
- On one hand, If we set up passwords complex to guess, they will be difficult to remember, on the other hand, if we choose to use passwords that are easy to remember, they will be easy to steal.
- People are more likely to use the same password for several different accounts. If a hacker steals the password, they will have access to the information for several accounts.
- We don’t really take into account the consequences of sharing our personal information… our lives on the Internet. The use of social networks can affect the security of our passwords. How? Very simply, many passwords are created using personal data, such as the name of our pets or the anniversary of a couple.
Due to all these issues, passwords are not secure anymore. Cyberattack hackers can easily steal passwords and gain access to people’s information.
To avoid this risk, we must consider other methods that are more difficult to hack. Next, we will discuss systems that use physiological and behavioural features as access keys, i.e. biometric identification systems.
Biometric identification systems: Facial recognition as a security system
Many industries implement biometric recognition systems for customer identity verification purposes. Although their effectiveness may be sometimes compromised by environmental conditions, hardware and the quality of the images captured, biometric authentication technology has significant advantages.
We will focus on the case of facial recognition as a security system. Why facial biometrics? Because it has certain advantages that make it stand out from the other options when it comes to identity authentication processes.
Facial recognition is one of the most robust biometric recognition systems. Human faces can be more discriminating and less intrusive and more usable than other systems as barely any active user collaboration is required.
Facial recognition is one of the most robust biometric recognition systems. The human face can be more discriminating than other features. Furthermore, the intrusive nature of this technology is very low as hardly any active collaboration from the user is required, which increases the degree of comfort.
Besides these differences compared to other biometric mechanisms, it also has other advantages that should be taken into account:
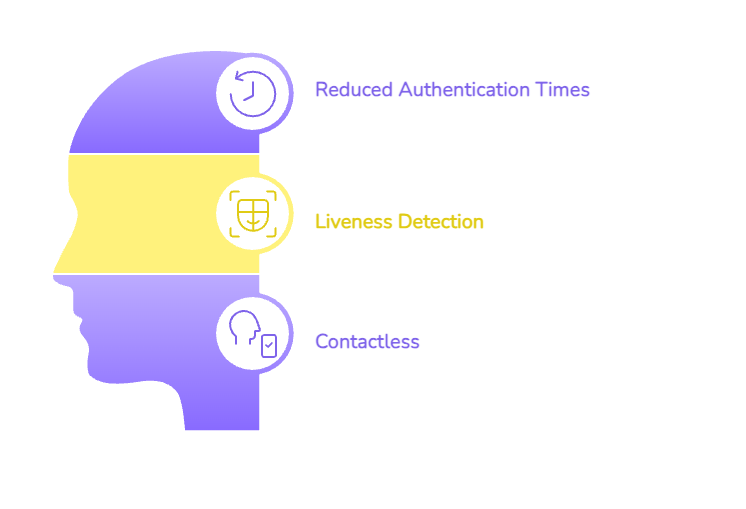
- Authentication times are reduced compared to traditional methods, resulting in improved user convenience and a better user experience.
- It is important to highlight the security controls that are associated with facial recognition technology. Pasive liveness detection measures can be performed in order to prevent fraud, verifying whether or not a real person is involved.
- When it comes to site access, this technology has a clear advantage allowing contactless access. It is not necessary to manipulate any equipment, just show your face.
Biometrics and two-factor authentication
One of the most frequent situations is the combination of both techniques (passwords + biometrics), what is known as ” two-factor authentication”.
Furthermore, smartphones with biometric sensors are encouraging the use of these systems in industries such as banking, FinTech and online gaming.
Another relevant issue to consider is that the coronavirus promoted the implementation of contactless measures, such us in ATMs, where money can be withdrawn minimizing contact through facial recognition.
Voice biometrics: A rising trend
Voice is another biometric approach that is gaining traction. Unlike facial recognition, voice biometrics relies on unique characteristics of a person’s tone, rhythm, and speech cadence. This method enables identity verification through audio-capturing devices, such as smart speakers or mobile phones, without requiring visual interaction.
This technology is particularly useful in scenarios where lighting conditions or privacy concerns might hinder other methods. Its integration into virtual assistants, telephone banking, and customer service platforms highlights its potential as either a complementary or alternative biometric solution.

Multimodal biometrics: The trend towards integration
A significant advancement in digital security is the use of multimodal biometrics, which combines several biometric authentication methods to provide more accurate and robust verification. This approach integrates technologies such as facial recognition and voice recognition, taking advantage of the strengths of each method to offset limitations that may arise in specific environments. For example, poor lighting can hinder facial recognition, while background noise can affect voice recognition. Nevertheless, by combining both techniques, the overall reliability of authentication is improved.
Multimodal biometrics not only enhances user experience by ensuring seamless and secure access but also reduces reliance on traditional methods that depend on memory or human factors. This integration increases the accuracy of identity verification and makes systems more accessible across various use cases. By merging multiple biometric data points, the integrity of security systems is strengthened, significantly decreasing the risk of fraud and verification errors.
This type of biometric technology can be customized to meet individual user preferences. As devices and digital environments evolve, having a flexible and adaptable authentication system becomes a crucial competitive advantage. By integrating various biometric techniques, we can create personalized security solutions that effectively address specific needs. This marks a significant milestone in the transformation of digital identity processes.
Looking to the future with objectivity
The path to advanced digital security does not require the immediate elimination of passwords; rather, it calls for a gradual transition where traditional and modern methods can converge to create hybrid and resilient systems. The integration of technologies such as facial recognition and voice biometrics ensures that security solutions remain adaptable in an ever-changing environment where protecting identity is increasingly critical.
It is essential to evaluate each step clearly in this transformation process. Biometric solutions aim for high levels of accuracy while striving to maintain a seamless user experience that feels natural. By combining multiple techniques, these systems can continue to operate effectively even if one method encounters challenges. This flexibility is vital as digital security threats grow more sophisticated and diverse.
The future of digital identity relies on innovation and collaboration among various technologies. The shift towards hybrid systems demonstrates that high levels of security can be achieved without sacrificing convenience or efficiency.
At Mobbeel, we develop solutions that facilitate this transition, such as MobbScan for digital onboarding and MobbID for biometric authentication. These solutions pave the way for identity protection that is as natural as recognising a face or hearing a voice, setting a new standard that meets the demands and challenges of the future.
If you are interested in our technology do not hesitate to contact us, and if you liked the article, share it and add value to your followers!

I’m a Software Engineer with a passion for Marketing, Communication, and helping companies expand internationally—areas I’m currently focused on as CMO at Mobbeel. I’m a mix of many things, some good, some not so much… perfectly imperfect.
GUIDE
Identify your users through their face
In this analogue-digital duality, one of the processes that remains essential for ensuring security is identity verification through facial recognition. The face, being the mirror of the soul, provides a unique defence against fraud, adding reliability to the identification process.