Living immersed in digital transformation, online tasks we perform on the Internet such as opening a bank account, signing an electronic contract, online training, shopping or working remotely are becoming increasingly challenging from a security point of view.
In this context, where technology advances by leaps and bounds, the user distrust’s in these online processes also grows, seeing them as vulnerable and insecure, mostly due to the growth of cybercrime.
For this reason, the European Union developed a legal framework called eIDAS (Electronic Identification and Signature) concerning electronic identification and trust services for electronic transactions in the EU, defining a common standard that provides greater confidence and security to online transactions between Member States and defines the different types of electronic signature, where the biometric signature stands out for its convenience and security.
Prior to the creation of this framework, there were no common policies within the EU regarding electronic identification, so companies and users had to adapt and meet national norms and regulations.
eIDAS: Electronic identification regulation in the EU
The EU Parliament and the Council of the EU adopted in July 2014 the Regulation Nº910/2014 (eIDAS) designed to create consistent regulations and standards across the EU for electronic identities and for trust services supporting authentication and signatures. This law repeals the previous directive established 15 years earlier (Directive 1999/93/EC), which already established a standard for electronic signatures.
On 29 September 2018, the compulsory mutual recognition of electronic IDs among Member States came into effect. On this date, all online public services using electronic identification at a high level must accept the electronic identification systems of other European countries.
This way, eIDAS fosters the confidence of consumers and SMEs by encouraging the use of identity verification services and removing barriers when it comes to secure online payments among EU Member States.
Apart from the electronic signature, eIDAS builds a regulatory framework for trusted services like time-stamping seals, electronic documents, mail certificates, as well as certificates for web authentication.
Therefore, the eIDAS regulation is very strict regarding the handling of personal data, since it allows the use of identification data exclusively for the explicit service requested.
What Types of Electronic Signatures are defined by Eidas?
The electronic signature acquires a great relevance within the regulation due to its massive use, its transversality to multiple industries and because we avoid identity theft and the use of paper.
Just as differing levels of physical signature verification are appropriate in different situations, there are also different digital signature levels:
- Electronic Signature,
- Advanced Electronic Signatures (the biometric signature is considered an advanced electronic signature) and
- Qualified Electronic Signatures,
To assess the suitability of each of them, we can consider the following parameters:
- Identification, the confidence you have that the person who signed is the actual person.
- Integrity, regarding document tampering. The document hasn’t been modified after it’s been signed.
- User experience, usability that enables the adoption of this technology.
- Authentication, verification that the signature has been undertaken by the signer.
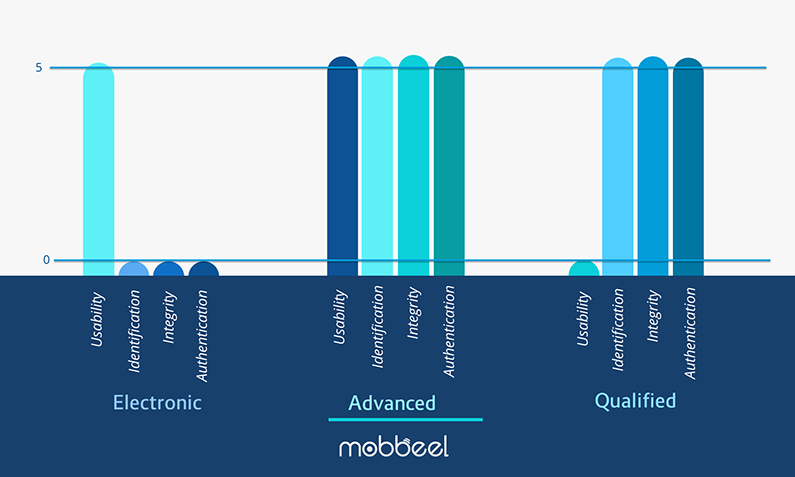
Electronic Signature
An electronic signature can be any kind of online or computerised signature where the signer accepts the conditions of the signed document, including an email message, a button accepting the clauses of a contract or a word processing document. It’s the generic idea, referring to the legal concept of signing something electronically.
The electronic signature does not require that the signature, or the acceptance by the signatory, is identified with the identity of a person. Furthermore, it is created under the unique control of the signatory, without any control of either the device used, the certificate or the system.
The way used sometimes to verify the signatory identity is through the email address used to send the document. Either way it is impossible to know who has really signed that document.
Advanced Electronic Signature
The Advanced Electronic Signature offers a higher level of security than the electronic signature and achieves the perfect balance between security and usability, while providing a great experience of use and legal validity.
An advanced electronic signature has to meet all the requirements established in Article 26, which at the minimum, must be:
- Uniquely linked to the signatory
- Capable of identifying the signatory
- Created in a way that ensures the signatory can maintain sole control
- Linked to the data it relates to in such a manner that any subsequent change to the data is detectable.
As competent authorities in the Member States currently use different formats of advanced electronic signatures to sign their documents electronically, it is necessary to ensure that at least a number of advanced electronic signature formats can be technically supported by Member States when they receive documents signed electronically.
Qualified Electronic Signature
Despite being the signature with more legislative power within the EU, it has never been used in a massive way because of its lack of usability and its dependence on hardware devices.
When it comes to signing, users need to have a qualified certificate, in addition to a device for creating a qualified signature, which must meet certain specifications.
Qualified trust services provide a stronger specific legal effect than non-qualified ones as well as higher technical security. Qualified trust services, therefore, provide higher legal certainty and higher security of electronic transactions.
Due to this need for requirements, the use of qualified electronic signatures is mainly reserved for procedures and applications with public administrations.
![]() A qualified electronic signature must meet all the requirements for an advanced signature, and in addition must be supported by a qualified signature creation device and a qualified public key certificate issued by a qualified TSP (trust service provider), what makes qualified signatures more stringent than the advanced ones.
A qualified electronic signature must meet all the requirements for an advanced signature, and in addition must be supported by a qualified signature creation device and a qualified public key certificate issued by a qualified TSP (trust service provider), what makes qualified signatures more stringent than the advanced ones.
![]() A qualified electronic signature must meet all the requirements for an advanced signature, and in addition must be supported by a qualified signature creation device and a qualified public key certificate issued by a qualified TSP (trust service provider), what makes qualified signatures more stringent than the advanced ones.
A qualified electronic signature must meet all the requirements for an advanced signature, and in addition must be supported by a qualified signature creation device and a qualified public key certificate issued by a qualified TSP (trust service provider), what makes qualified signatures more stringent than the advanced ones.
Our biometric signature as Advanced Electronic Signature
The biometric signature captured with procedures based on MobbSign which electronically collects unique biometric data from each individual to securely associate them with the content of an electronic document, meets the legal requirements in order to be considered as an advanced electronic signature, in the terms defined by Article 26 in eIDAS, because it allows to identify the signatory and detect any further change on the signed document.
Mobbeel can help you with the digital transformation of your business model, bringing technologies to the market, such as the biometric signature with legal validity and user verification during digital onboarding processes.
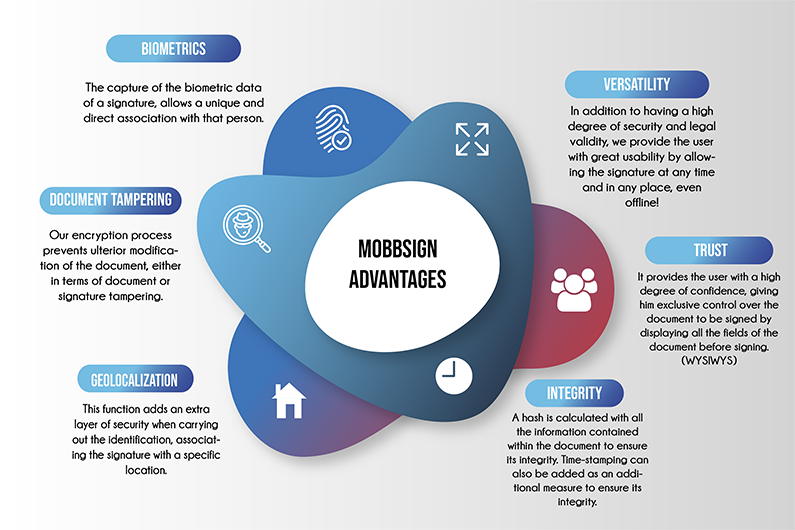
Some of the advantages of using MobbSign – our biometric signature solution – are:
- MobbSign gives users the versatility to sign a contract in any place and at any time, even in offline locations since the process is fully offline. This makes the signature process more secure since it does not dissociate the signature from the document in order to travel to any server, avoiding any malicious user intercepting it.
-
It is contactless technology. Our biometric signature solution allows viewing a PDF document on the user’s mobile screen, and signing it using their own device, without the need for physical contact. Since the entry of the coronavirus, the need for this type of technology to prevent infections has increased.
- A hash is calculated with all the information contained within the document. This hash can then be used to validate the document’s integrity (i.e. that it has not been altered since it was signed). Even If the client wishes to perform the integration with a time-stamping authority, this hash is sent to the chosen TSA, which offers an extra integrity layer.
- All the biometric information provided by the user’s signature (time, position, the pressure of each point, etc.) is unambiguously linked to them, and are taken to reproduce, in case of future claims, the way in which the user signed as well as validate its authorship. The biometric information of the signature is stored, according to the ISO 19794-7, in order to facilitate the future interoperability of this data with any verification tool.
- It also includes the location where the document is signed (GPS).
If you are interested in learning more about what our digital signature do, please do not hesitate to contact us!

I’m a Software Engineer with a passion for Marketing, Communication, and helping companies expand internationally—areas I’m currently focused on as CMO at Mobbeel. I’m a mix of many things, some good, some not so much… perfectly imperfect.
PRODUCT BROCHURE
Discover our biometric signature solution
Provide your customers with the option to easily and ecologically sign documents anywhere and anytime using our biometric signature, which is considered an Advanced Electronic Signature with full legal validity.




